Configuring a VNC based Graphical Console for a Xen Paravirtualized domainU Guest
| Previous | Table of Contents | Next |
| Creating and Booting a Xen Guest domainU using an NFS Mounted Root Filesystem | Running and Connecting to VNC Servers on a Xen Guest (domainU) System |
| Purchase and download the full PDF and ePub versions of this Xen eBook for only $8.99 |


|
So far in Xen Virtualization Essentials we have focused on running Xen domainU systems using just the text based console to interact with the system. It is not uncommon, however, to need to view and interact with a graphical desktop environment running on the guest operating system. This can be achieved using one of two technologies known as SDL and VNC. Probably the most flexible option is that provided by VNC.
In terms of displaying graphical desktop environments for a Xen guest, VNC offers two approaches. The first approach (covered in this chapter) involves using VNC capabilities that are built into the Xen guest domain (domain0) to view and interact with the virtual frame buffer (vfb) of the domainU system. A second option is to run one or more VNC servers directly on the domainU system and connect directly to those servers. This approach will be covered in the next chapter (Running and Connecting to VNC Servers on a Xen Guest (domainU) System).
What is VNC?
VNC is an acronym for Virtual Network Computing and essentially provides remote access to graphical desktop environments. The system consists of one or more VNC servers running on a remote system and VNC viewers running on a local system. The VNC server runs the graphical desktop on the remote system and transmits the appearance of the desktop to the VNC viewer. The VNC viewer in turn transmits user interactions with the desktop to the VNC server where they are relayed to the desktop environment. VNC uses compression algorithms to speed the display process and is supported on a wide range of platforms. This makes it possible, for example, to display a Linux desktop environment on a remote Windows system.
The VNC server and viewer components can communicate over any network connection including the internet allowing desktops to be accessed from anywhere in the world where an internet connection is available.
VNC Security
Before proceeding it is important to note that VNC itself does not include any security measures. If a default VNC session is used over the internet, therefore, the session is susceptible to eavesdropping. It is, however, possible to use secure tunneling techniques to protect VNC sessions. Both the secure and insecure methods of using VNC will be covered in this chapter.
Configuring a Xen domainU for VNC Access
In this chapter it is assumed that you have a Xen domainU system configured and are able to boot this system using the Xen text based console. If this is not the case return the Table of Contents and pick a method from those listed to configure and install a Xen domainU system.
Assuming you have a working text based Xen guest system, VNC access can be enabled by adding a single line to the Xen domainU configuration file:
vfb = [ 'type=vnc' ]
This is the most basic of configuration options and will set up VNC access to the next available VNC port (starting at port number 5901) with no password access. To specify a specific port number and password add vncdisplay and vncpassd directives to the vfb line:
vfb = [ 'type=vnc,vncdisplay=10,vncpasswd=s3cr3t' ]
When the guest system boots up it will be accessible to the VNC viewer on port 5910 and access will be granted if s3cr3t is entered at the password prompt.
With the appropriate change made to the configuration file boot the system as usual, being sure to use the -c command-line option so that the text console is also available during the boot process.
Connecting to the Guest Desktop using VNC Viewer
This section assumes that the desktop environment of the Xen domainU system is not being accessed over an insecure and unencrypted network (such as the internet). This approach is only safe for accessing the domainU desktop either from the Xen host or from a system on the same trusted network. For details on secure remote desktop access refer to the appropriate sections later in this chapter.
If no vncdisplay port number was specified on the vfb = configuration directive and no other Xen guests or VNC sessions are running, then the desktop is likely to be accessible on port 5901. Therefore, to access this display run the following command:
vncviewer <IP Address of Xen Host>:5901
where <IP Address of Xen Host> is the IP address or host name of the Xen host system on which the guest domainU system is running and not the IP address of the domainU guest. The reason for this is that we are accessing the desktop via VNC services provided by domain0 on the host and not by VNC servers running on the guest. For details on running and accessing VNC servers on a domainU guest read the chapter entitled Running and Connecting to VNC Servers on a Xen Guest (domainU) System. If vncviewer is being run on the Xen host then localhost will suffice. If vncviewer is running on a remote client then it is strongly recommended that the connection be established through a secure SSH tunnel as described later in this chapter.
If a port number was specified using the vncdisplay= directive then this port needs to be specified. For example, the following command assumes that vncdisplay 10 was specified in the configuration file and consequently connects to port 5910 on the local system:
vncviewer localhost:5910
If a password was specified in the Xen domainU configuration file then vncviewer will prompt for this before the graphical console is displayed:
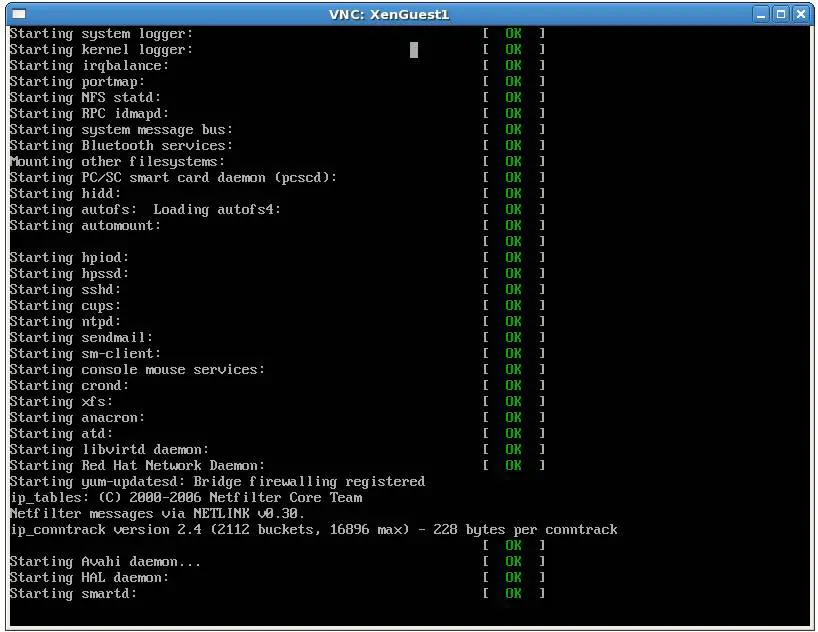
Assuming that vncviewer is able to connect to the server the graphical console will appear. Note that at this point no desktop is running so all that will be displayed is output from the boot process of the domainU guest. The following figure shows a typical graphical console before a desktop environment has been launched:
The next step is to start a desktop environment.
Starting a Graphical Desktop on the Xen domainU Guest
At this point we have successfully configured a Xen domainU guest system to provide a VNC graphical console access via domain0 on the host system. The domainU guest has booted and we have successfully connected to the to the VNC session using vncviewer. The next step is to start a desktop environment running on the domainU system such that it appears in our vncviewer window.
At this point both the Xen text console and the vncviewer window should be visible. If the Xen text console is no longer attached to the domainU guest attach it as follows:
xm console guestname
where guestname is the name of the domainU guest system. Log in to the domainU guest at the Xen console as a suitable user. Once logged in, the default desktop environment for the domainU guest system can be launched using the startx command:
startx
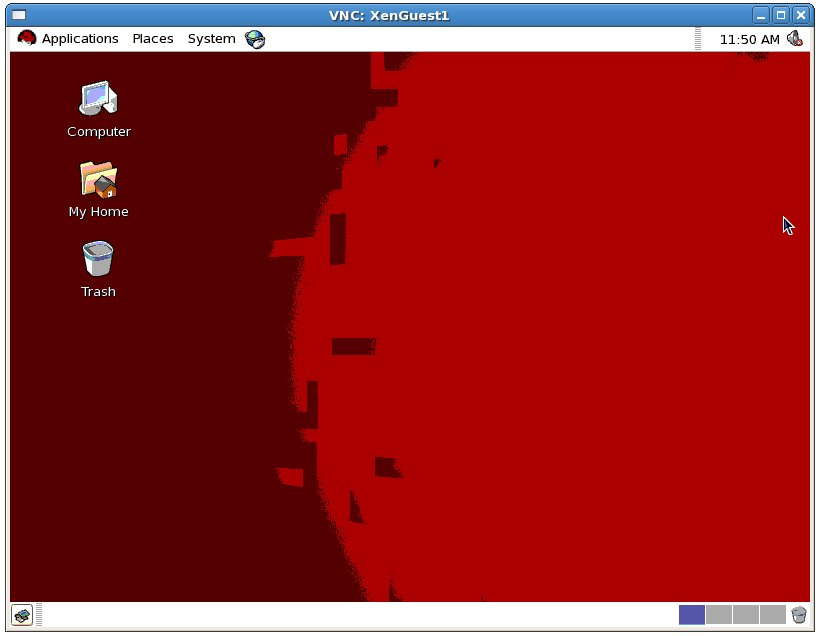
After a short delay and a number of diagnostic messages in the Xen text console, the graphical desktop environment will appear in the vncviewer window. The following figure shows a Red Hat Enterprise Linux GNOME desktop running inside the vncviewer window:
Establishing a Secure Remote Desktop Session
The remote Xen desktop configurations we have explored so far in this chapter are considered to be insecure because no encryption is used. This is acceptable when the remote connection does not extend outside of an internal network protected by a firewall or when the connection is taking place on the Xen host system. When a remote session is required over an internet connection a more secure option is needed. This is achieved by tunneling the remote desktop through a secure shell (SSH) connection.
Before a secure connection is established the SSH server must be installed in the desktop to which the connection is to be established and the firewall configured to allow SSH access. This is the default for many Linux distributions but may not be the case for your distribution. If in doubt refer to the documentation for your chosen distribution to find out how to install and enable SSH access.
Once the SSH server is installed and active it is time to move to the other system. At the other system, log in to the remote system using the following command, which will establish the secure tunnel between the two systems. The following example assumes that vncdisplay number 10 (which maps to port 5910) was specified in the domainU configuration file. Modify this value to suit your environment:
ssh -l username -L 5910:localhost:5910 hostname
In the above example, hostname is either the hostname or IP address of the remote system and username is the account you wish to use to log in. Enter the password associated with the specified account when prompted. The secure connection is now established and it is time to launch vncviewer so that it uses the secure tunnel. Leaving the ssh session running in the other terminal window, launch another terminal and enter the following command:
vncviewer localhost::5910
As before, the vncviewer session will prompt for a password if one was specified in the domainU configuration file, and then launch the VNC viewer providing secure remote access to your Xen domainU guest desktop environment.
If you are connecting to the remote desktop from outside the firewall using Network Address Translation (NAT) keep in mind that the IP address for the ssh connection will be the external IP address provided by your ISP, not the internal LAN IP address of the remote system (since this IP address is not visible to those outside the firewall). You will also need to configure your firewall to forward port 22 (for the ssh connection) to the IP address of the system running the desktop. It is not necessary to forward port 5910. Steps to perform port forwarding differ between firewalls, so refer to the documentation for your firewall, router or wireless base station for details specific to your configuration.